BLUESPAWN is an active defense, endpoint detection, and response tool designed for quick detection, identification, and elimination of malicious activity and malware across a network. The tool encourages user participation and contribution; suggestions for new features, bug reports, and development assistance are welcomed through their Discord server.
The creation and open-sourcing of BLUESPAWN were driven by several motivations. The developers aimed to create a tool that could rapidly identify malicious system activity, understand their detection coverage precisely, gain a better comprehension of the Windows attack surface, and contribute to the open-source Blue Team Software. BLUESPAWN also aims to demonstrate features of Operating System APIs by leveraging a wealth of resources like Microsoft Documentation and StackOverflow Answers, which may benefit other developers.
Modes
BLUESPAWN is composed of three primary modes. These modes, which include various submodules (some of which may not yet exist in the codebase) are at different stages of planning, research, and development. They are also supported by several other modules.
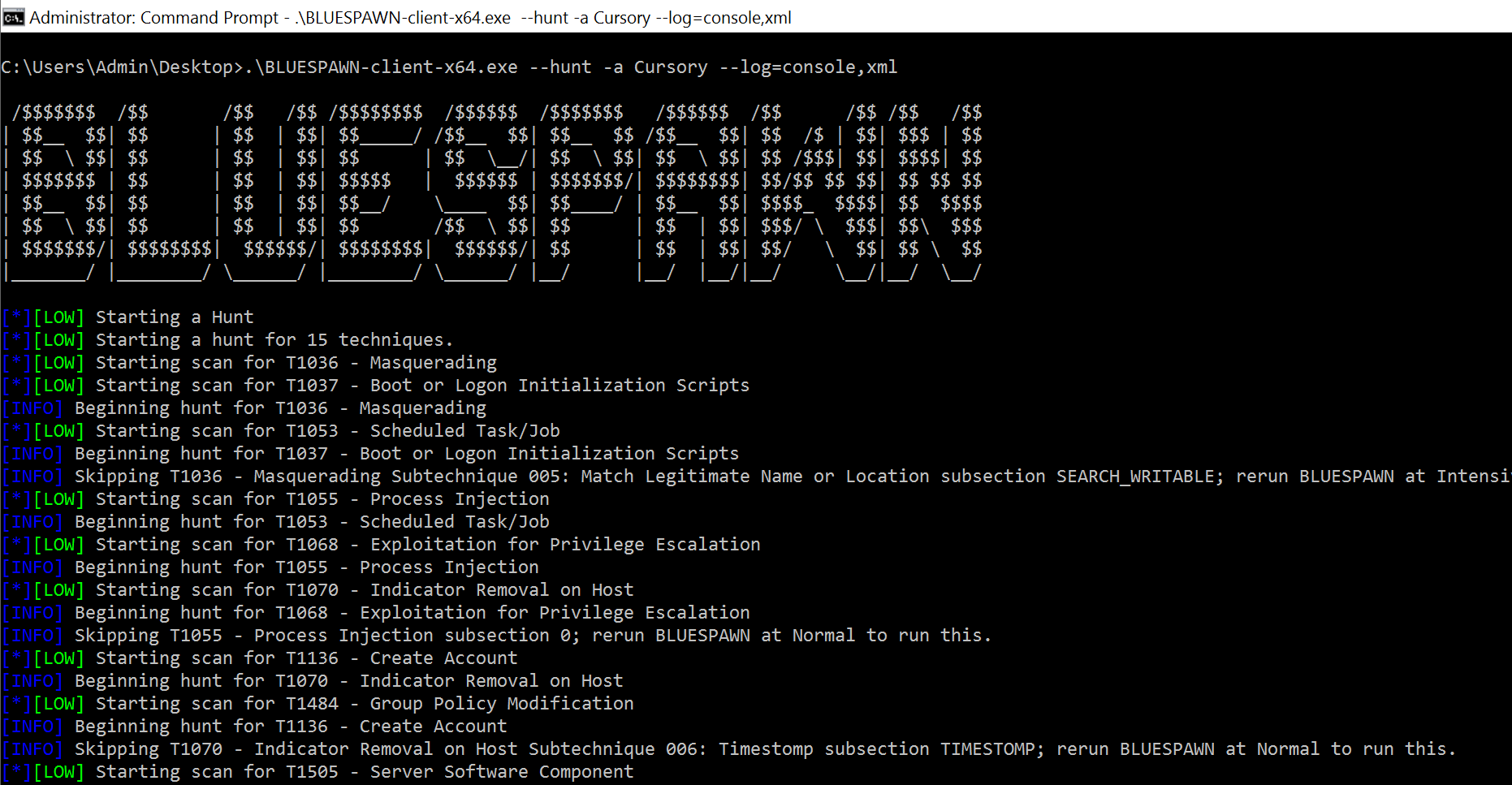
- Hunt: Searches for signs of malicious activity
- Mitigate: Applies security settings to reduce vulnerabilities
- Monitor: Constantly observes the system for potential malicious actions
- Scan: Evaluates items found during hunts to determine if they are suspicious or malware
- User: Includes the main program, IOBase, and other similar functions
- Util: Includes a set of modules that support the main operations such as Configurations, Event Logs, File System, Log, PEs, and Processes
Features
- Open-source
- Easy to use
- Fast
- Active defense and endpoint detection
- Real-time monitoring against active attackers
- Contains three primary modes: Hunt, Mitigate, Monitor
- Scan feature to evaluate items found during hunts
- User features including the main program and IOBase
- Util features for supporting main operations, such as Configurations, Event Logs, File System, Log, PEs, and Processes
License
The App is released under the GPL-3.0 License
Resources & Downloads
As an avid healthcare blog with a deep focus on open-source technologies for healthcare and education, we excited to share some top-notch open-source HIPAA-compliant tools that are transforming the landscape of healthcare app development.
While this post will focus on the open-source techs, our next posts will focus on several
Open-source software (OSS) has become an integral part of the technology landscape, offering numerous benefits but also presenting unique challenges, especially in the healthcare sector.
This post explores the history, advantages, and potential risks associated with OSS, with a particular focus on its application in healthcare.
What is Open-Source Software
In a world where technology constantly grows and cyber dangers spread, startups in cybersecurity need to move through an environment that is always changing. As the number of cyber threats keeps going up, more and more startups dealing with cybersecurity are entering this market. Interest from investors is also increasing;
In a nutshell, digital transformation is the process where digital technology is used in integrating all business processes. This alters the way in which business operations are carried out to add more value to its customers.
Digital transformation is not a mere shift from an analog to a digital enterprise;
The healthcare industry handles a massive amount of personal and private information about patients. We're talking medical records, insurance details, and more – a goldmine for bad guys looking to steal and misuse this sensitive data. That's why healthcare IT professionals play a super important role in
twert - a Free and open-source Self/Parental control program for Windows
If you have ever been concerned about the security of your MacOS device, you will be pleased to learn about macOS-Fortress.
This powerful tool is a combination of firewall, blackhole, and privatizing proxy for trackers, attackers, malware, adware and spammers. It provides kernel-level, OS-level, and client-level security, making your MacOS
What is the FatRat?
TheFatRat is an exploitation and pentesting tool designed for educational purposes. It has the capability to compile malware with popular payloads, which can then be executed on various platforms including Windows, Linux, Mac, and Android.
This makes it a versatile tool for understanding the dynamics of